Zero-day vulnerability appeared in open source dev tool for Kubernetes
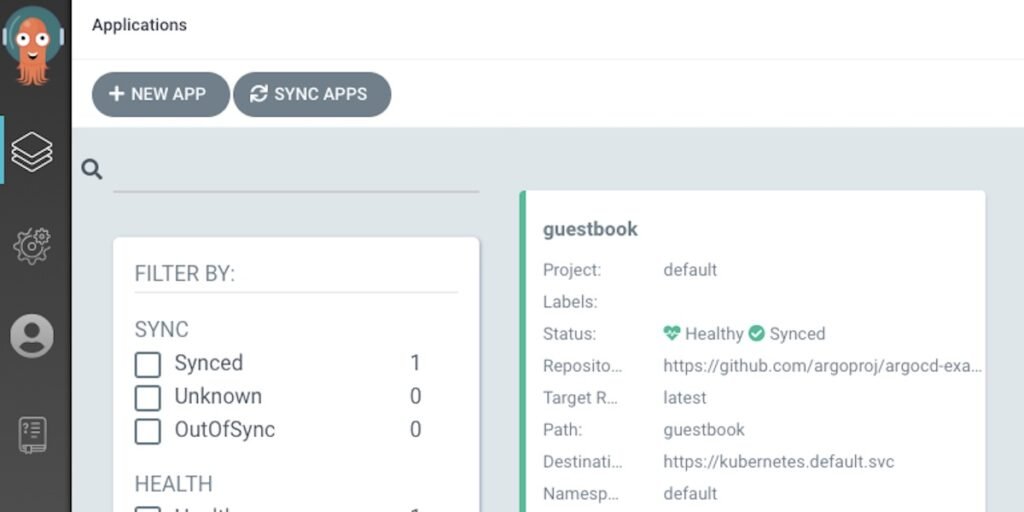
Researchers today discovered a zero-day vulnerability within Argo CD, open-source software for developers for Kubernetes and Kubernetes, that has a “high” severity rating.
The flaw (CVE-2022-24348) was discovered by the Apiiro research team. cloud-native application security firm Apiiro. Apiiro claims to have disclosed the vulnerability to the open-source Argo project before revealing the vulnerability in their blog today. Updates are now available, Apiiro announced.
Argo CD is a continuous delivery platform for developers who make use of Kubernetes, which is the main container orchestration platform.
Exploits of the vulnerability in Argo CD could allow an attacker to acquire sensitive information–including passwords, secrets, and API keys–through the utilization of malicious Kubernetes Helm Charts, said Moshe Zioni, vice president of security research at Apiiro, in the blog post. Helm Charts comprise YAML files that handle Kubernetes applications.
Zioni confirmed that the vulnerability has been assigned a severity rating as “high” (7.7), however, as of the time of writing NIST’s National Institute of Standards and Technology (NIST) website was not yet displaying the severity rating.
In an email sent to VentureBeat, Zioni said the security flaw could result in the potential to have a “very significant impact on the industry” because Argo CD is used by many organizations. The open-source project boasts more than 8.300 rating stars at GitHub.
Argo CD is an Argo CD platform that provides explicit specifications for applications and automated deployments that rely on GitHub According to Intuit. Intuit gave this project to the Cloud Native Computing Foundation in 2020 after it acquired Applatix, the creator of the platform Applatix in the year 2018.
Potentially dangerous
The flaw that was recently disclosed of Argo CD “allows malicious actors to load a Kubernetes Helm Chart YAML file to the vulnerability and ‘hop’ from their application ecosystem to other applications’ data outside of the user’s scope,” Zioni stated in an Apiiro blog entry.
So the attackers “can read and exfiltrate secrets, tokens, and other sensitive information residing on other applications,” Zioni said. A breach of this vulnerability could trigger privilege escalation and lateral movement and the disclosure of sensitive information Zioni stated in his post.
Files for application “usually contain an assortment of transitive values of secrets, tokens, and environmental sensitive settings,” he explained. “This can effectively be used by the attacker to further expand their campaign by moving laterally through different services and escalating their privileges to gain more ground on the system and target organization’s resources.”
Zioni claimed Zioni said that the Argo CD team gave a “swift” response after being aware of the vulnerability.
Open source insecurity
The discovery of the flaw in Argo CD comes amid increasing concern about the widespread use of supply chains that are not secure. The most prominent incidents include security breaches like the SolarWinds and Kaseya attacks, while general attacks on software supply chains grew to more than 30% by the year 2021. Aqua Security reported.
Additionally, open-source vulnerabilities like the many vulnerabilities in the Log4j logging library of Apache and the Linux polkit program have highlighted the vulnerability. On Monday, the Open Source Security Foundation announced an initiative to protect the supply chain. It is funded by $5 million of Microsoft as well as Google.
“We are seeing more advanced persistent threats that leverage zero-day and known, unmitigated vulnerabilities in software supply chain platforms, such as Argo CD,” said Yaniv Bar-Dayan Co-founder and CEO of cybersecurity risk management company Vulcan Cyber, in an email to VentureBeat.
“We need to do better as an industry before our cyber debt sinks us,” Bar-Dayan stated. “IT security teams must collaborate and do the work to protect their development environments and software supply chains from threat actors.”
Research Snipers is currently covering all technology news including Google, Apple, Android, Xiaomi, Huawei, Samsung News, and More. Research Snipers has decade of experience in breaking technology news, covering latest trends in tech news, and recent developments.