How To Create A Password Policy
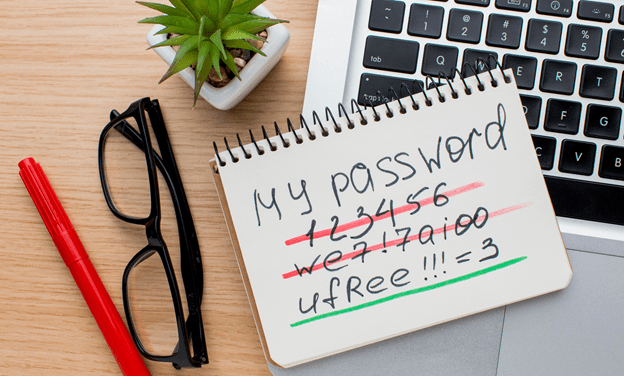
Password policies are tricky to get right. If you make them too complex, the users won’t be able to follow them or remember their passwords. If you make them too simple, you put your network at risk.
So, how can you strike that balance without making it too complicated?
We’ve compiled a list of things to consider when creating your policy to keep everyone happy.
Define Your Complexity
Password complexity is the first consideration when creating a password policy. How long should your users make their passwords, and what characters are required?
A minimum password length of eight characters is usually recommended as it’s long enough to be secure and short enough to remember. The longer the password, the more difficult it is to crack. User training should encourage longer passphrases.
Incorporating characters into a password, including numbers and symbols, increases the complexity and makes it harder to brute-force.
While you shouldn’t type existing passwords into this, Kaspersky released a password checker to help you compose secure passwords and phrases.
Account Lockout Parameters
The next thing to consider is how many chances you give users to get their passwords right. Restricting access to a user or system account after a specific number of wrong attempts is the most effective way of protecting against hackers or nefarious characters trying to access your network.
Specify in your policy how many attempts your users can have within a specific timeframe before they need to contact your IT support team. You can also allow them to unlock automatically after a particular time to make it easier for accidental triggering to be undone.
Make sure your users know this number; when passwords are changed, they change it in all locations. One of the most common reasons for account lockouts is a stray, unchanged password in a phone’s email settings.
Since password management is essential for improving security and protecting sensitive data, it’s in your best interest to invest in an enterprise password vault that stores passwords, certificates, and other credentials for shared business accounts and systems in a secure, IT-managed location.
Expiration?
Password expiry is a controversial topic in cyber security. Some argue that it’s not beneficial for businesses to require passwords to expire as it leads to patterns (Looking at you, incremental numbers!).
Setting passwords to expire after a specific time can also increase security when it comes to unknown breaches. Plus, some industry standards, such as ISO 27001 and PCI, require password expiration for compliance.
It’s a personal choice but one that needs internal consultation. It depends on your user base and how they interact with your network. Regularly review your decision and make sure you’re considering the changing employees and that their training is up to date with the correct policy.
Written Policy vs Technical Settings
Finally, you’ll need to decide how to put this into effect. Depending on your company setup, you may be able to use cloud security tools to configure technical settings and automatically apply your policy settings. It would be best if you also had a written policy with all current policy settings defined clearly to cover the passwords you cannot control technically. Users will have company accounts on all sorts of websites and systems you cannot control.
Research Snipers is currently covering all technology news including Google, Apple, Android, Xiaomi, Huawei, Samsung News, and More. Research Snipers has decade of experience in breaking technology news, covering latest trends in tech news, and recent developments.












